ETM automatically learns SAP usage patterns of your organization
It uses this information identify suspicious activity and to eliminate false positives.
As the result, your security operations team saves valuable time.
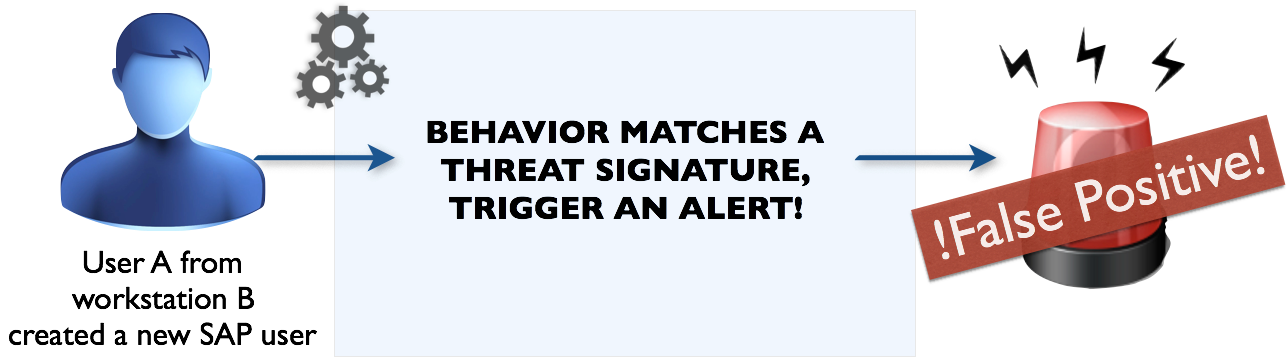
SAP systems are noisy. This results in static enterprise threat detection signatures to be ineffective during daily operations
Static threat detection signatures trigger many false positives. The false positives cost time and effort to eliminate as seen in the picture on the right.
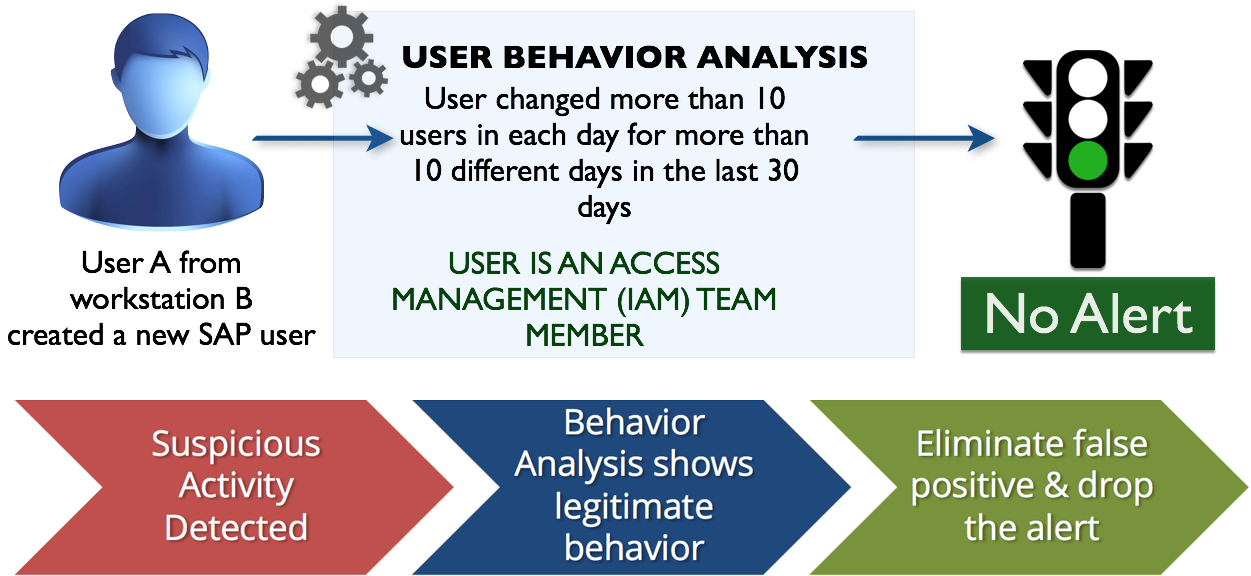
Adaptive Noise Reduction utilizing user behavior analysis eliminates false positives
Enterprise Threat Monitor’s Adaptive Noise Reduction engine analyzes SAP activity information based on machine learning and common usage patterns. This results in understanding the organization specific patterns, and user types, eliminating false positives without user intervention.
The picture on the left shows detection of a member of identity and access management team of an SAP customer.
ETM identifies that the user pattern “changing multiple user passwords in a day for many days in a month” is an indication of legitimate behavior. In this case ETM identifies that more than 10 user passwords for more than 10 times in a month results in this classification. Depending on the organizational usage pattern, these thresholds may differ.
This results in utilizing more time for focusing on real SAP incidents and less time for false positives
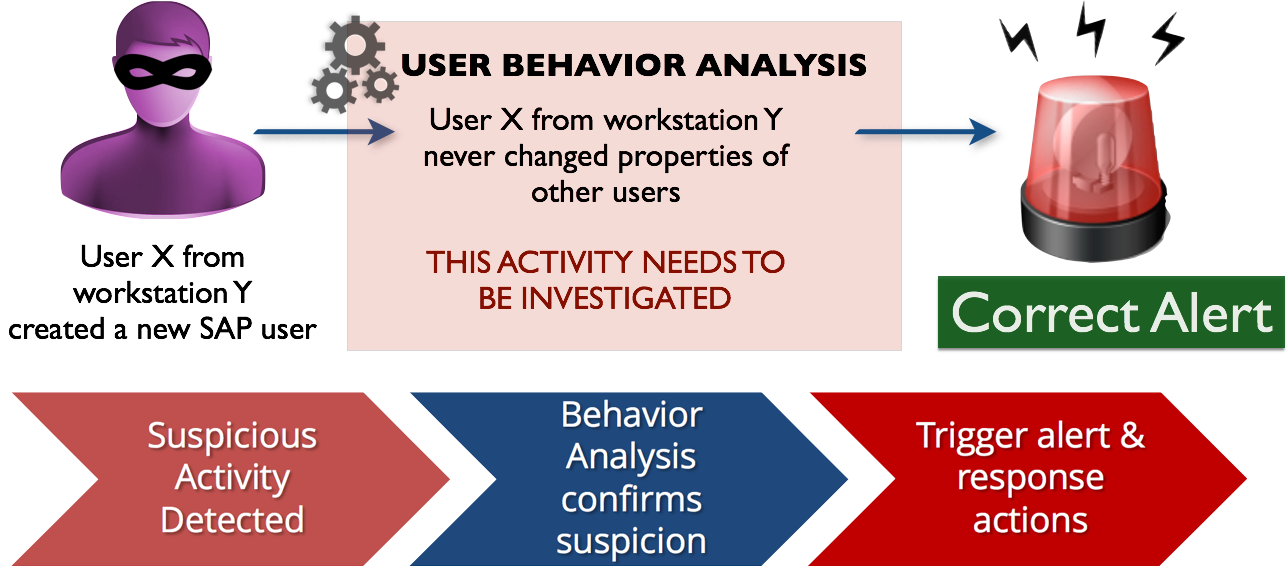
By eliminating the false positives, SOC teams can focus on the real incidents more efficiently. On the picture right, this a malicious user who obtained privileges for user creation, and exploited it. It is discovered by Enterprise Threat Monitor.
Recent real-world implementation: How ETM eliminated over 98.1% of the false positives!
The real-life SAP SIEM implementation problem: Too many matches!
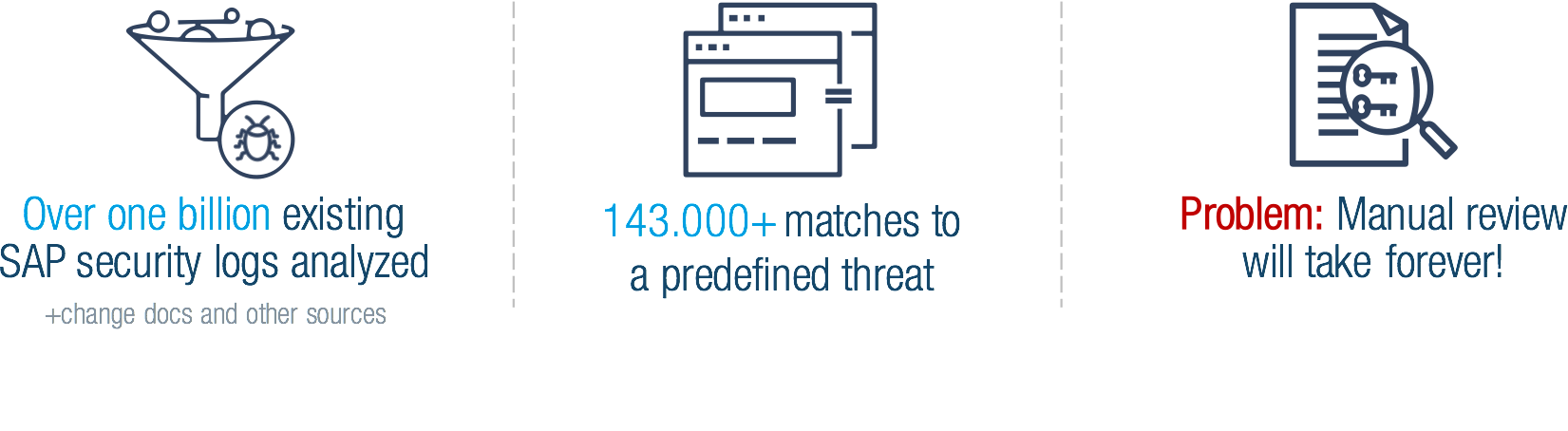
At a recent customer implementation Enterprise Threat Monitor analyzed SAP security logs of over 50 SAP systems:
Based on the results, it was clear that it would not be possible to review incidents if false positives cannot be eliminated.
Solving the Problem: Enterprise Threat Monitor Adaptive Noise Reduction eliminated 98.1% of noise
By utilizing machine learning and ETM’s propriety algorithms, Enterprise Threat Monitor discovered that 1,105 patterns match to a legitimate user behavior, resulting in eliminating 98.1% of the detected threats.
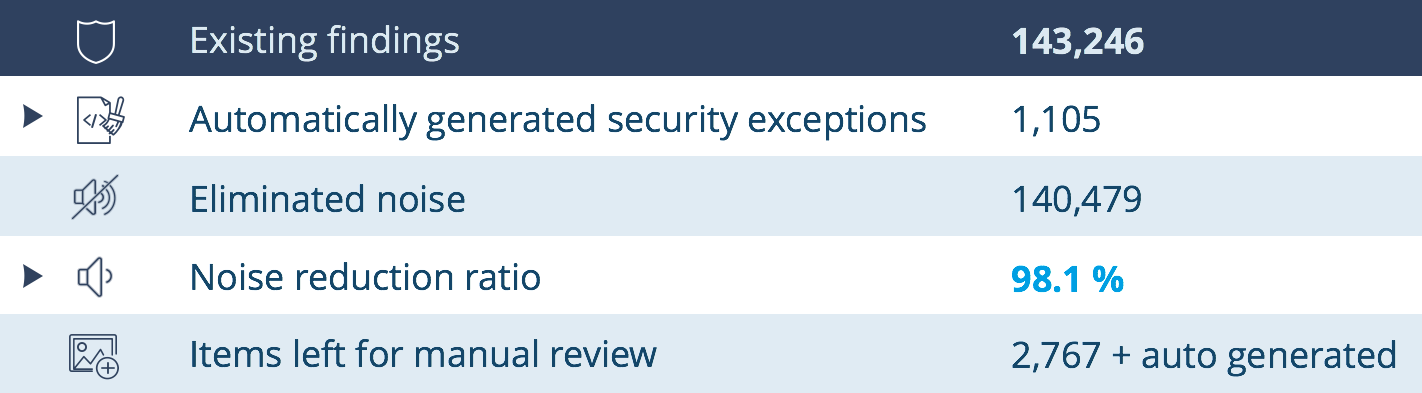
After manual review of the machine generated security exceptions, the customer verified all security exceptions to be correct. ETM saved the customer over 130 MD of manual work for reviewing and configuring the security exceptions.
