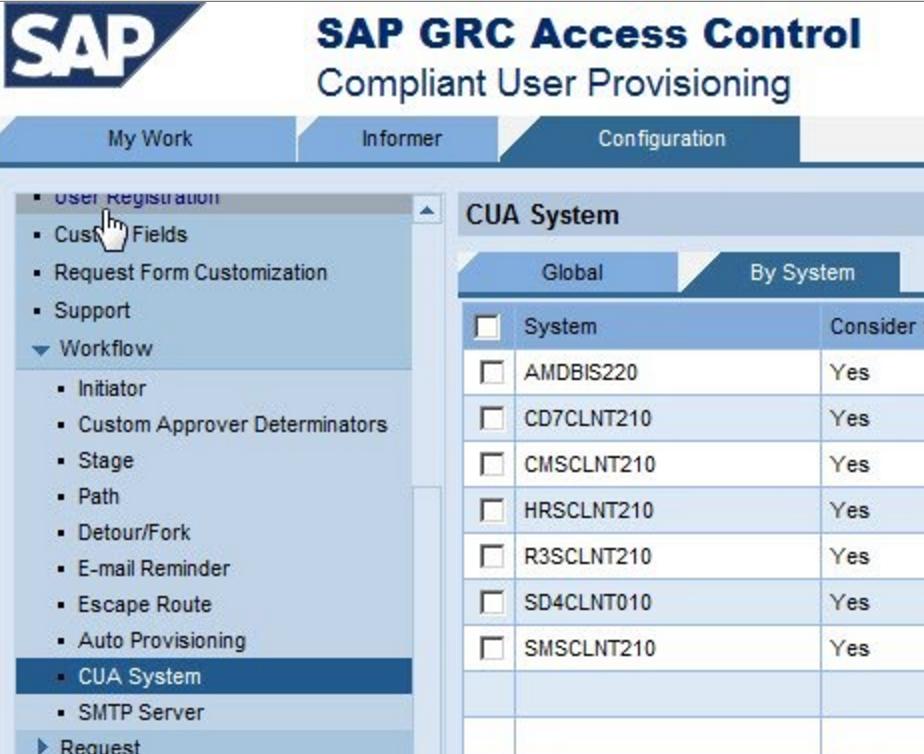
SAP GRC is a critical SAP application, which allows security management functions including provisioning of users and roles in an enterprise.
If an attacker compromises the SAP GRC system, it can severely impact the organization resulting in theft of customer information, manipulation of bank transfers, damaging the SAP systems, and causing downtime.
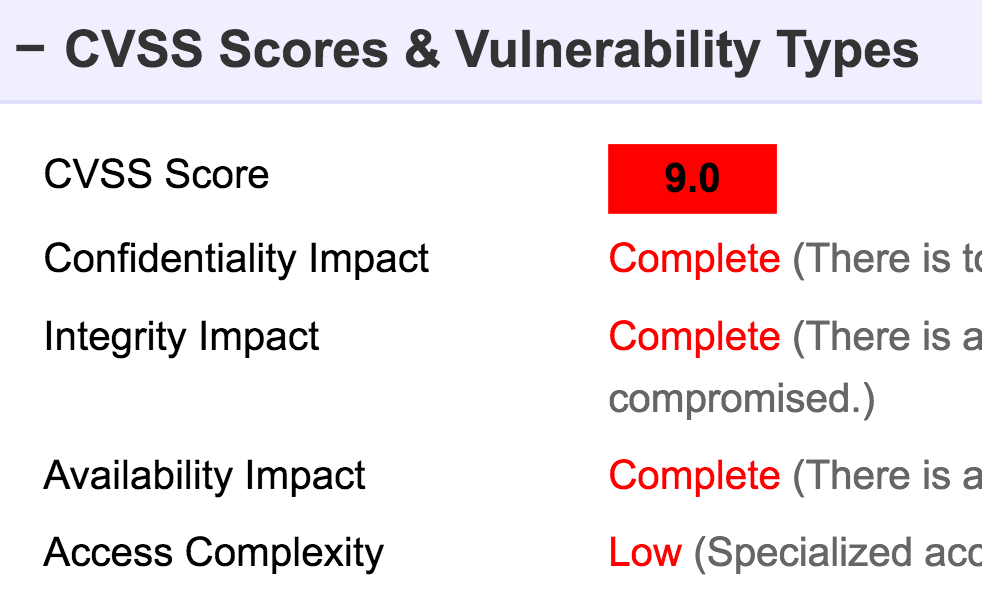
In 2013, ESNC researchers uncovered several remotely-exploitable vulnerabilities in SAP GRC, which are rated as 9.0 out of 10 by NIST (https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2013-3678).
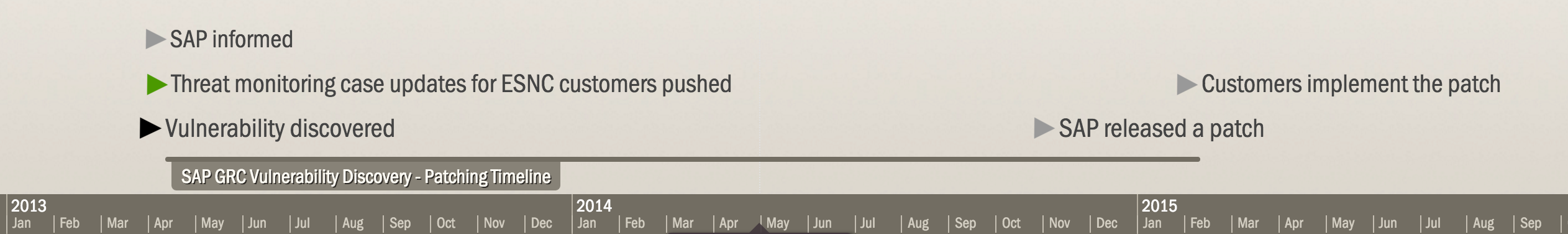
ESNC informed SAP about the details of the vulnerabilities and confirmed that SAP has received the information. ESNC provided all required information to SAP for fixing the issues.
At the same time, ESNC engineers released attack signatures for these SAP vulnerabilities and distributed them to ESNC Security Suite customers (Note: ETM is previously named ESNC Security Suite R01) .
As soon as ESNC released the attack signatures, ESNC customers had a safety net against misuse of the SAP GRC vulnerabilities. The rest of the world had to wait until a patch is released and during this time (more than 18 months) their systems were vulnerable.
Just before beginning of 2015, SAP released the patch (SN 2039348).
ETM protects SAP customers from many zero-days similar to this example. The ESNC research team identifies vulnerabilities and zero-days, follows publications and conferences and uses this information to build and distribute SAP-specific attack signatures for ETM.
Based on ESNC’s research and collaboration with SAP SE, more than 100 SAP security vulnerabilities are identified and patched. At an average, it took SAP more than a year to patch the vulnerabilities.
Furthermore, ETM also includes attack detection signatures for 3rd party SAP add-ons such as OpenText/IXOS, XFT and others.
SAP GRC Vulnerability Disclosure Timeline